In today’s digital world, cyber threats are evolving rapidly, posing significant risks to businesses of all sizes. From ransomware attacks that lock businesses out of their critical systems to phishing scams that exploit unsuspecting employees, the dangers of cybercrime are real and increasingly sophisticated.
The Rising Tide of Cyber Threats
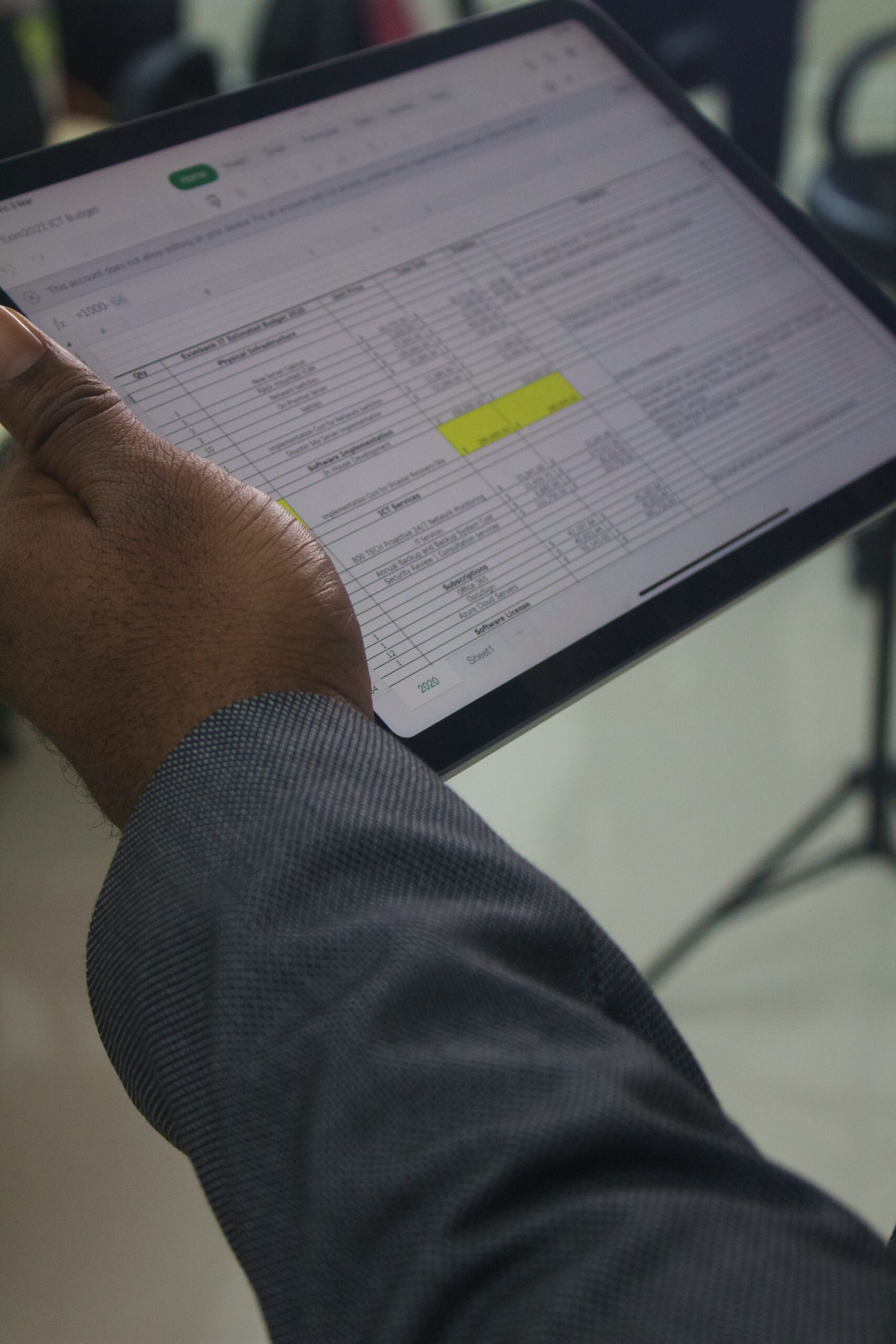
Cybersecurity expert Scofield Thomas of 800 TECH recently discussed the alarming rise of cyberattacks in Trinidad and Tobago during an interview titled The Digital World with Keron Rose. One of the most pressing concerns is ransomware, where hackers infiltrate a system, lock access to critical data, and demand a ransom, often in cryptocurrency to restore access. Businesses caught unprepared face severe disruptions, revenue loss, and reputational damage.
Beyond ransomware, institutions in the region have faced data breaches, locking them out of crucial systems. Hackers don’t just attack randomly, they monitor systems, assess vulnerabilities, and strike at the most opportune moment. The shift from physical security threats to digital ones requires a new approach to safeguarding businesses.
The Digital Evolution of Security
Gone are the days when securing a business meant installing burglar-proof gates and alarm systems. Today, businesses must think digitally. Just as physical security evolved with technological advancements, cybersecurity must be prioritized to protect modern assets.
Firewall protection acts as a digital security guard, monitoring and preventing unauthorized access. Intrusion detection systems work like alarm systems, alerting businesses to unusual activities. Endpoint protection solutions help detect and respond to potential threats before they escalate.
Why a Cybersecurity Blueprint is Critical
Businesses must take proactive steps to protect their digital assets. A cybersecurity blueprint is a structured approach to identifying risks, implementing protective measures, and preparing for cyber incidents. Key components include:
- Identifying Critical Assets – Determine what data, systems, and workloads are mission-critical.
- Assessing Risks – Understand vulnerabilities and the potential impact of cyberattacks.
- Implementing Security Measures – Deploy firewalls, multi-factor authentication (MFA), and endpoint detection solutions.
- Creating a Response Plan – Establish protocols for responding to cyber incidents, ensuring minimal disruption.
- Regular Training and Simulations – Conduct ongoing cybersecurity awareness training for employees to mitigate risks from phishing and social engineering attacks.
Small Businesses Are Not Immune
A common misconception is that only large corporations are targets for cybercriminals. In reality, small businesses with weak security measures are prime targets. Cybercriminals often exploit businesses that rely solely on platforms like Google Drive, Microsoft OneDrive, and social media without additional security protocols.
Even simple measures, such as using encrypted email systems, implementing MFA, and conducting regular security training, can significantly reduce risks. Consulting with cybersecurity experts can help small businesses establish an affordable and effective security strategy.
The Next Steps
Every business leader should ask their IT team a crucial question: If we get hacked today, what happens next? If the answer is unclear or unconvincing, it’s time to take action. Implementing cybersecurity tabletop exercises—where key personnel walk through emergency response scenarios, ensures preparedness when an attack occurs.
As cyber threats continue to evolve, businesses must adapt and fortify their defenses. Ignoring cybersecurity is no longer an option; it is a necessity for survival in today’s digital age.
For expert cybersecurity guidance, contact us to learn how to secure your business in 2025 and beyond.
Our Blog
AI Is Transforming Business. But Is Your Security Keeping Up?
Artificial Intelligence is no longer a futuristic concept. It is rapidly reshaping how businesses operate across Trinidad and the Caribbean. From predictive analytics and automated workflows to intelligent customer support, AI enables companies to optimize...
Strengthening Cybersecurity in the Caribbean
In the fast-evolving world of cybersecurity, it’s crucial for businesses to stay ahead of the curve when it comes to protecting their data. Junior Gilpin, Senior Cybersecurity Engineer at 800 Tech and a certified Data Protection Officer, shares invaluable insights...
Exciting Update: Our New Commitment to Cybersecurity for SMEs
We're thrilled to announce a significant transformation in our services! Starting January 2024, we have shifted our focus from general technology support to a specialized commitment to cybersecurity for small and medium-sized enterprises (SMEs). This strategic change...
Elevating Your Cybersecurity
In an era dominated by technology, cybersecurity isn't just a buzzword; it's a critical necessity. The modern business landscape demands a proactive approach to protecting your data and infrastructure from an ever-evolving threat landscape. 🚀 Why You Need to Take...
Innovative Solutions for Enhanced Productivity!
A valued client recently approached us with a unique challenge: the need to boost employee productivity while ensuring accurate time and billing management. They'd explored various off-the-shelf solutions but couldn't find one that perfectly aligned with their...
The Power of Structured Databases: Why Excel Isn’t Always the Best Choice
While Excel remains a valuable tool for basic data organization, it may not always be the optimal choice for storing and collating large, complex datasets. Structured databases offer scalability, data integrity, security, efficient analysis, collaboration, and long-term maintenance capabilities that can enhance productivity and enable data-driven decision-making.
Unleashing Business Potential: Join Us to #BridgetheGap and Experience Positive Transformation
At 800 TECH, we believe in empowering businesses to unlock their full potential and bridge the gap to a more streamlined and successful future. By joining forces with us, you can experience a range of positive transformations that will propel your business towards new...
Transforming Trinidad and Tobago’s Financial and Export Sector with 800-TECH
Once upon a time, in the vibrant financial and export sector of Trinidad and Tobago, an organization had been making its mark for over three decades. As a pioneer in the industry, they faced the challenge of outdated technology that hindered their operations. It was...
Bridging the Gap: Conquering Technology Fears – A Three-Step Strategy
In today's rapidly evolving digital landscape, the divide between technology and businesses has become a significant challenge, particularly in the financial sector. Many businesses are hesitant to embrace technology due to their fear of the unknown. While financial...