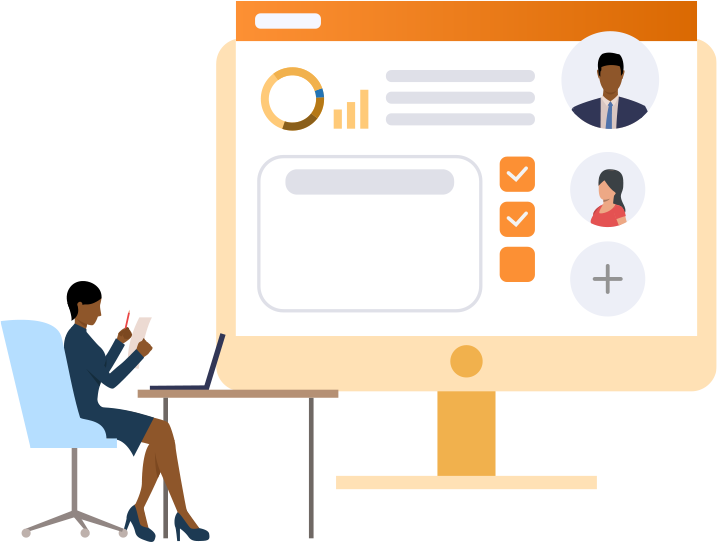
If you still do not have a comprehensive HRM solution, let me introduce you to our 360HRM software.
360HRM is our Human Resource Management application that is used to aggregate employee data within the organization. The integrated workflows allows for ease of data retrieval and collaboration with real-time analytics based on your business objectives.
It consists of seven key modules, where each module is customized based on the needs of an organization. This customization is achieved during the Business Process Re-engineering (BPR) exercise (refer to a past blog post about BPR). During this exercise, each client ‘s culture and business processes are carefully analyzed. This information is harnessed and utilized to create organization specific workflows to ensure the transition of company culture while ensuring policy compliance.
HOW FLEXIBLE IS 360HRM?
The brilliance of 360HRM is its intuitive user-friendly interface which minimizes the learning curve for employees. All modules are fully customizable enabling a smooth digital transition bridging the gap with familiarity of forms, workflows and reporting guidelines, thus significantly minimizing an employees’ learning curve. The flexibility created within each of the seven modules makes for an amazing user experience. The modules are:

Employee Management – 360HRM Employee Management module simplifies the management of employee’s data. It securely captures and accesses all sensitive employee data from anywhere in the world. Consisting of crucial work-related and important personal information about each employee. In a nutshell, it is an online inventory of an employee’s life cycle within your organization.
This robust module enables:
- Employee onboarding.
- Research employee history
- Modification of employee records
- Off-boarding employees at the end of their work history.
Incident Management – is the process of identification, analysis, and implementing corrective actions to prevent future re-occurrences. Managed incorrectly, incidents can quickly escalate into disaster including loss of life. Our incident management module limits the potential of disruption caused by events. Without effective incident management, an incident can disrupt vital business functions or damage critical human resources. In most organizations incidents are a regular occurrence, how you manage these incidents are critical in ensuring these events don’t become disruptive to your business. Our incident management module has been carefully coded to:
- Capture new incident with supporting documents
- Track and report on workplace incidents
- Monitor departmental incident metrics
- Create a repository of knowledge for risk assessment
- Mitigate against future risk.

Employee Requisition Management – Finding the right talent is a key component in ensuring your business strategy. Recruitment is never an easy process, it can be time consuming but essential to finding the right fit for business. This is why we created the Employee Requisition Management system which enables organizations to maintain a database of applicants, track and manage job openings, and more. The easier it is to manage and access candidate information, the faster job openings will be filled.
In the Leave Management module, what we’ve taken into consideration is the different ways in which vacation can be accumulated. In some companies, vacation is accumulated based on the hierarchical structure in the organization, the more senior you are in a company the more vacation you’re entitled to. Therefore, the vacation leave component is structured to facilitate these differences. In other organizations vacation is based on longevity, the longer you’ve been employed with the company, the more vacation you’re entitled to, therefore the module will be customized to suit a longevity environment. And finally, in some organizations, there is a fixed amount of vacation, and that construct is also coded into the fabric of the application.
The productivity of any organization hinges heavily on how it manages the leave of its employees. 360HRM Leave Management system simplifies the management of your employee’s. It allows the organization to manage employee time-off, setup leave policies, and track the status of leave requests inclusive of supporting documents.


Overtime Management – Overtime Management is one of those crucial functions that can have an adverse effect on profitability if not managed well. 360 HRM Overtime Management module packs a heavy punch in creating a structure for tracking employee overtime requests and approvals. The data derived from Overtime Management reports provide key insight into an organization’s decisions.
Performance Management – Retaining great employees is just the first step in growing your business. Providing feedback so they can grow with the organization and become part of the culture is equally important. 360 HRM Performance Management module allows your organization to track performance and measure Key Performance Indicators (KPI). This module assists in creating a robust workforce that suits the demands of the organization.
This scientific tool is used to measure employees overall impact based on key performance indicators. It is also a critical benchmarking instrument which signals when retooling and retraining may become necessary to bring employees back into alignment with the vision and mission.


Security Management – As with any structured application we have created the admin center where all users within the organization are administered. The Security Management module is the core of the 360HRM where employee permissions are administered in tandem with the organization’s HR policies and organizational structure. The authorization groups and effective permissions are as follows:
- Executive – Full functionality and visibility of 360HRM
- Management – Monitor & manage departments subordinates including reports
- Supervisor – Management of employees
- Employee – Leave, performance management (other levels as directed by management)
We are scheduling demos of the 360HRM and you can be one of the first organizations to witness this. Schedule a consultation by clicking on the link below.
Our Blog
SaaS Security Risks: The Hidden Threats Lurking in Your Business Applications
Many businesses invest heavily in cybersecurity. However, one of the biggest threats often remains hidden in plain sight. Forgotten software subscriptions, abandoned user accounts, unused integrations, and overlooked cloud applications can quietly expose organisations...
Cloud Data Security: Why Your Cloud Is Talking and You Need to Listen
Cloud data security has become a critical concern for businesses of all sizes. While organizations continue to store increasing amounts of data in the cloud, many still lack full visibility into where that data is, who can access it, and how it is being used. As...
Business Email Compromise in the Age of AI: The New Cyber Risk
Business Email Compromise in the Age of Artificial Intelligence (AI): What Every Organization Needs to Know Business email compromise is rapidly evolving, and organizations can no longer afford to treat it as just an IT issue. Instead, it must be recognized as a...
Hidden Email Threats: How to Protect Your Business
Hidden email threats are becoming more sophisticated every day, and businesses across the Caribbean are feeling the impact. As a result, organizations must stay alert, informed, and proactive. In this article, we’ll explore the rise of hidden email threats, how they...
Your Inbox Is a Crime Scene: Why Email Visibility Is the First Line of Cyber Defense
Your inbox is a crime scene and most businesses do not even realize it. Every day, thousands of malicious emails attempt to infiltrate organizations of every size. While firewalls and antivirus software are important, they are not designed to fully secure your email...
Business Email Compromise: How to Prevent Email-Based Fraud
Business Email Compromise (BEC): The Cyber Threat Hiding in Plain Sight When people think about cybercrime, they often imagine highly technical attacks; hackers breaking into systems using complex tools and advanced code. However, the reality is far simpler and far...
Breaking Barriers in STEM: Confidence, Identity & Career Advice
There are pivotal moments in a student’s journey when learning moves beyond theory and becomes personal. That was the experience for third-year university women in STEM who attended a powerful empowerment workshop entitled Breaking Barriers in STEM, facilitated by...
Cybersecurity Mistakes- The Costliest Mistakes Companies Make
Discussion on The Costliest Cybersecurity Mistakes Companies Still Make and how to fix them Featuring insights from Junior Gilpin, Senior Cybersecurity Engineer, 800 TECH on the radio programme the Digital World. Cybersecurity today is no longer a “technology issue.”...
End-of-Year IT Housekeeping- Tighten Up Security in December
Scofield Thomas, Managing Director of 800TECH, and Keron Rose on radio programme the Digital World: End-of-year is full of excitement including leave plans, office parties, school events, family dinner; the whole vibe is ease up and exhale but IT Housekeeping is one...